Every vulnerability was written by a human.
So why is all your security downstream of that moment?
Think about how most security budgets are actually spent.
- Scanners that analyse code after it's written.
- Pentests that find vulnerabilities after they've shipped.
- WAFs that intercept attacks after the code is already live.
All of it operates after the damage is done.
And all of it creates a dynamic where the security team is permanently chasing the engineering team.
Adding friction, creating bottlenecks, and still never getting ahead of the problem.
The moment that actually creates the vulnerability - a developer writing a flawed line of code - receives almost no attention at all.
Fixing a vulnerability before it ships costs 40× less than fixing it in production.
Source: NIST - Cost of Software Security Defects
Most Security Budgets
Alert
Code
Training
Code
Interactive Cybersecurity Training
Personalized
Program
Your developers choose the programming language and the framework they use daily.
Vulnerable
Playground
A vulnerable application with the chosen framework is deployed just for the developer.
Real-World
Risks
They learn about real world vulnerabilities. Vulnerabilities we saw regularly during penetration tests.
Hands-On
Hacking
They exploit these vulnerabilities like a real hacker would, so that they understand the risks.
Security
Solutions
They learn how to fix these vulnerabilities, and implement the fix in the source code.
Continuous
Security
Their fix is deployed on the server, and Their application becomes a little more secure each time.
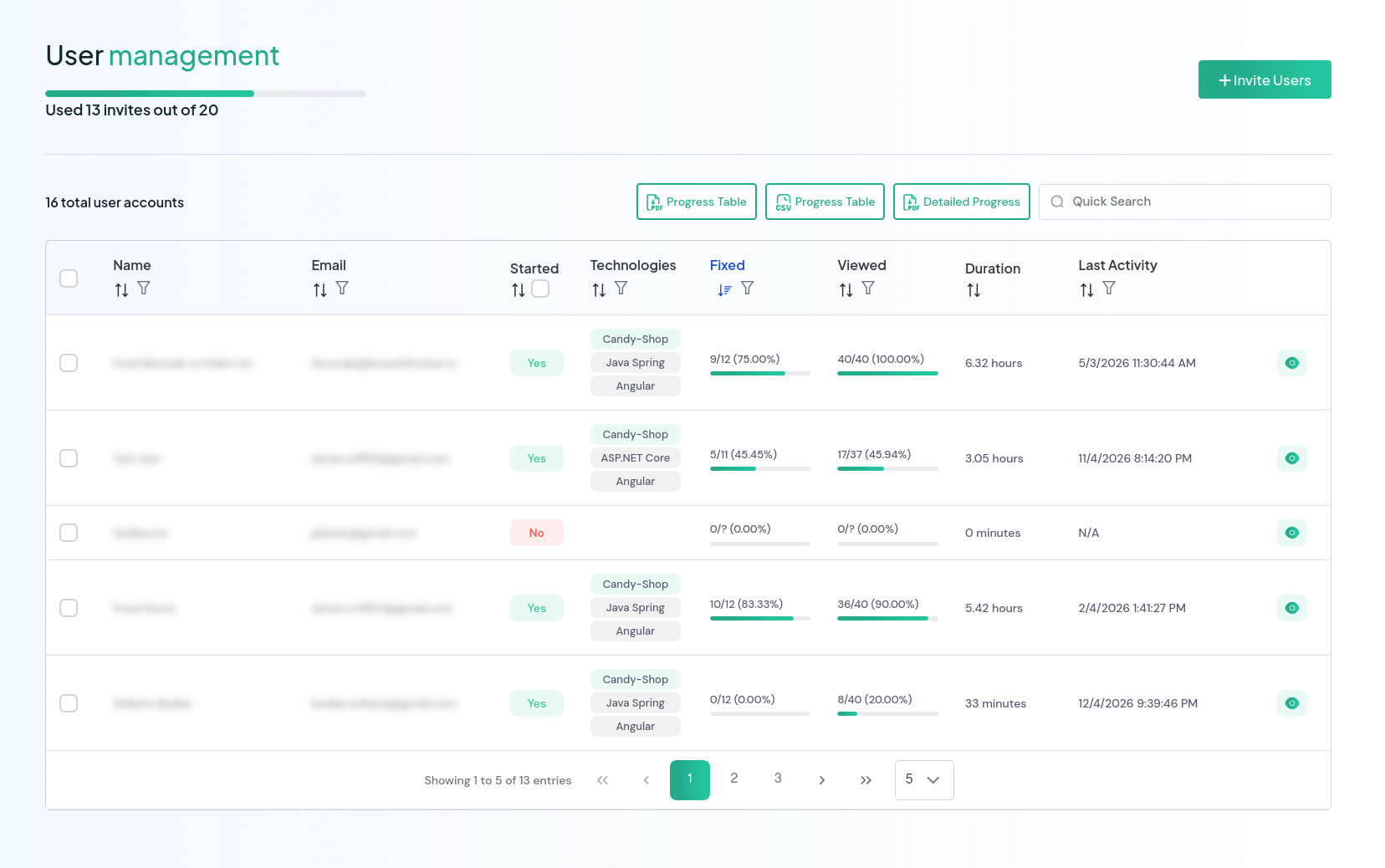
Your Compliance Audit Trail, Built In
From day one, you have full visibility into your team's training, and a complete audit trail ready to produce at any moment. No chasing. No spreadsheets. No coordination overhead.
Invite your entire team in one click
Import your developer list and send invitations in a single action. Each developer self-onboards, chooses their stack, and gets a private vulnerable application deployed automatically.
A complete audit trail in one click
Every training action is timestamped and logged. Before an audit, during a regulatory review, when an enterprise client asks for proof, you produce a complete, signed PDF record in one click. Who trained, when, what they fixed.
Your Compliance File, Completed for You
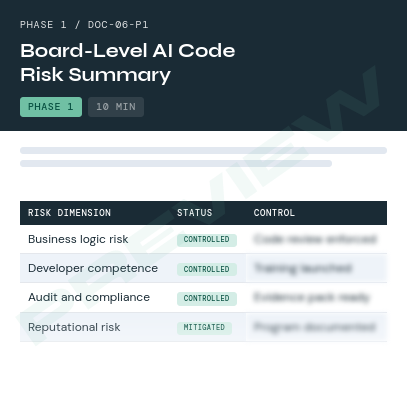
Most training programs hand you a completion certificate and leave you to figure out the rest. Devsecurely goes further.
After the training, we compile the full documentation package your auditors actually need:
- Training scope document: a formal description of the program your team completed, the OWASP Top 10 vulnerability classes covered, and the methodology used
- Individual completion certificates: one per developer, timestamped, naming the specific training completed and the stack trained on
- Team completion summary: an aggregated report showing which developers completed training, when, and their verification scores
- Vulnerability coverage map: a document showing which OWASP categories were covered and how each was verified by the platform
- Auditor-ready formatting: the entire pack is structured to satisfy the documentation requirements of PCI-DSS, SOC 2, ISO 27001, and GDPR out of the box
A Developer's Blueprint to Workstation Security
A hardened application deployed from a compromised workstation is still a compromised application.
Securing a developer's machine isn't the same as securing a standard office laptop.
Developers have specific needs that generic IT security policies don't account for:
- Elevated permissions to run local servers and containers;
- Specialised tools like package managers, debuggers, and proxies;
- Direct access to production credentials, API keys, and SSH access to infrastructure.
Lock down those tools the wrong way and you don't get a secure developer. You get a developer who can't work.
This guide is written specifically for developer workstations. It shows how to harden the attack surface that generic IT policies ignore, without removing the permissions or tools your developers actually need to do their job.
Before/After Security Skills Assessment
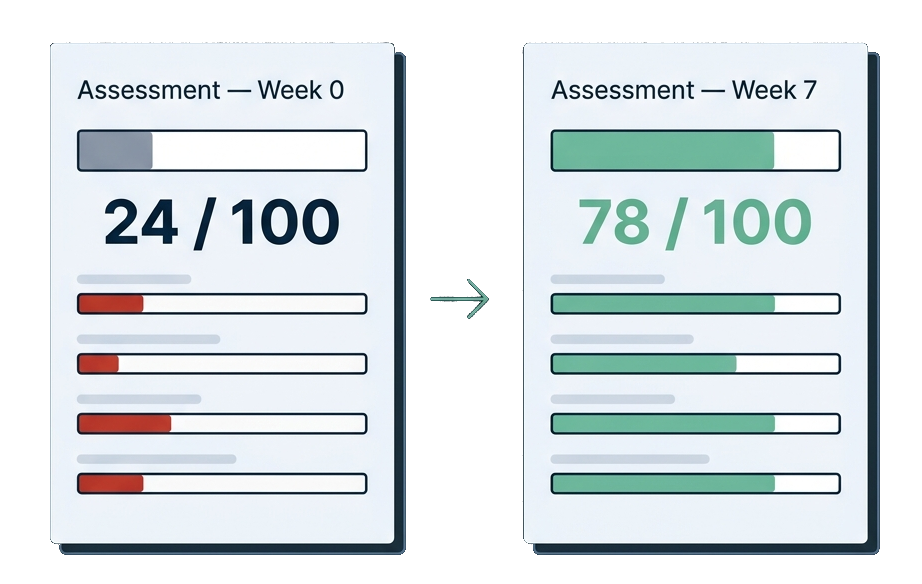
A scenario-based assessment administered before and after the programme, producing a measurable skills score per developer.
Quantifiable proof that the training worked. Available to early clients at no additional cost.
Who Built This

Imed Bounab
- ✓8+ Years in Penetration Testing
- ✓Advised CAC 40 Security Teams
- ✓Trained 40+ Development Teams
In my third year of college, I built a website from scratch.
No frameworks. Just me, a blank editor, and the particular euphoria of refreshing a browser and seeing something appear that didn't exist an hour ago.
I started creating content, SEO traffic picked up, and a small community formed.
I felt like I built something real.
Then one day, a comment appeared on one of my articles:
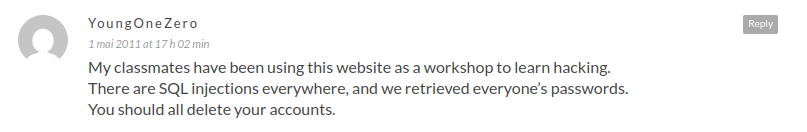
The community I had spent months building disappeared over the next few days.
And I sat there, a developer who had just learned the hard way, that writing code and writing secure code are two completely different things.
I spent the next several years learning everything those teenage hackers knew, and more.
I enjoyed it so much that I made a career out of it. I became a penetration tester, an ethical hacker. And over 10 years I audited hundreds of real applications across every major industry.
What I found, consistently, was this: the difference between developers who write vulnerable code and those who write secure code wasn't talent. It was a way of thinking.
Developers who wrote secure code think differently. And that way of thinking can be taught.
That's what Devsecurely is built on.
And it's why I know this training works: not because I studied security from the outside, but because I was the developer who didn't know what he didn't know, until it was too late.
From Booking to Certified...In One Working Week.
Four steps. No IT overhead. No preparation required on your end.
Book the planning call
We confirm your team's stack, size, and timeline. Your Security Kickoff session gets scheduled.
Your team attends the Kickoff
Live, tailored to your stack. If it delivers, we activate the full programme. If not, full refund.
Your team goes live
Invitations sent. Developers self-onboard. Private vulnerable apps deployed automatically.
Certified on OWASP Top 10
Every vulnerability class fixed in real code. Certificates issued. Audit trail complete.
After the next few sprints, you either have more vulnerabilities in your codebase, or fewer.
What changes that outcome is the decision you make today.
We are confident in everything on this page.
That's because we have seen what happens to development teams after a Security Kickoff session. We've watched it change how they write code in real time.
And if you're skeptical, good. Skepticism is how you got to a senior security role.
That's exactly why we built the guarantee the way we did. You don't commit to anything until you've seen it work.
If after the Kickoff session you're not 100% certain this will change your team, you get a full refund. On the spot.
But just know this: no company has asked for that refund yet.
Book the call. Your life as a security leader is about to get a little simpler.